How to enforce 2 Factor Authentication on user login?
Enforce 2fa on user login
Overview: This article provides an overview of Two-Factor Authentication (2FA) implementation options: enforcing 2FA globally for SSH and web interfaces, and selectively for user groups, along with configuration instructions and method setup details.
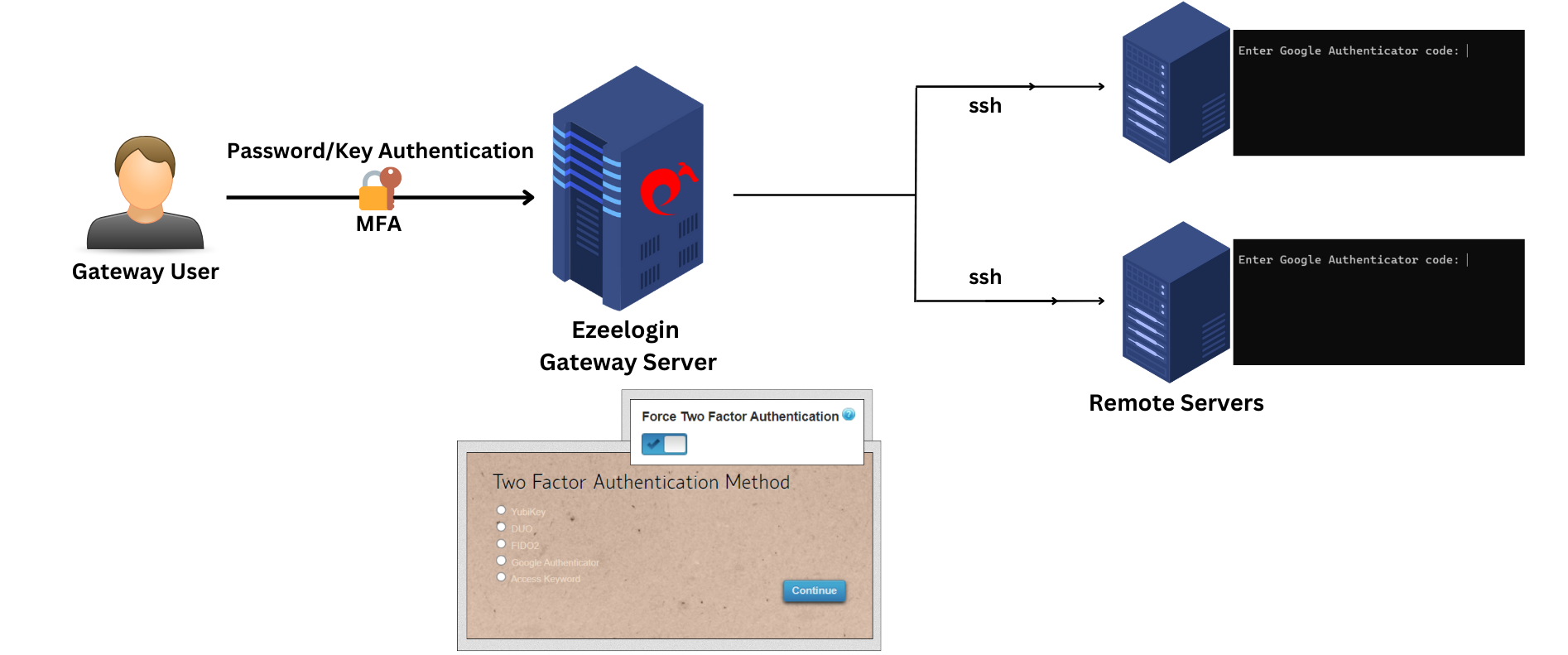
You have two options for implementing Two-Factor Authentication (2FA) for user logins:
1. Enable 2FA for all users globally.
2. Implement Two-Factor Authentication (2FA) for designated user groups as per their specific requirements and access levels.
1. Enable 2FA for all users globally.
Enable the force 2fa to enforce Two-Factor Authentication (2FA) for both Ezeelogin backend (ezsh) and the web interface, requiring all users to use 2FA globally for added security.
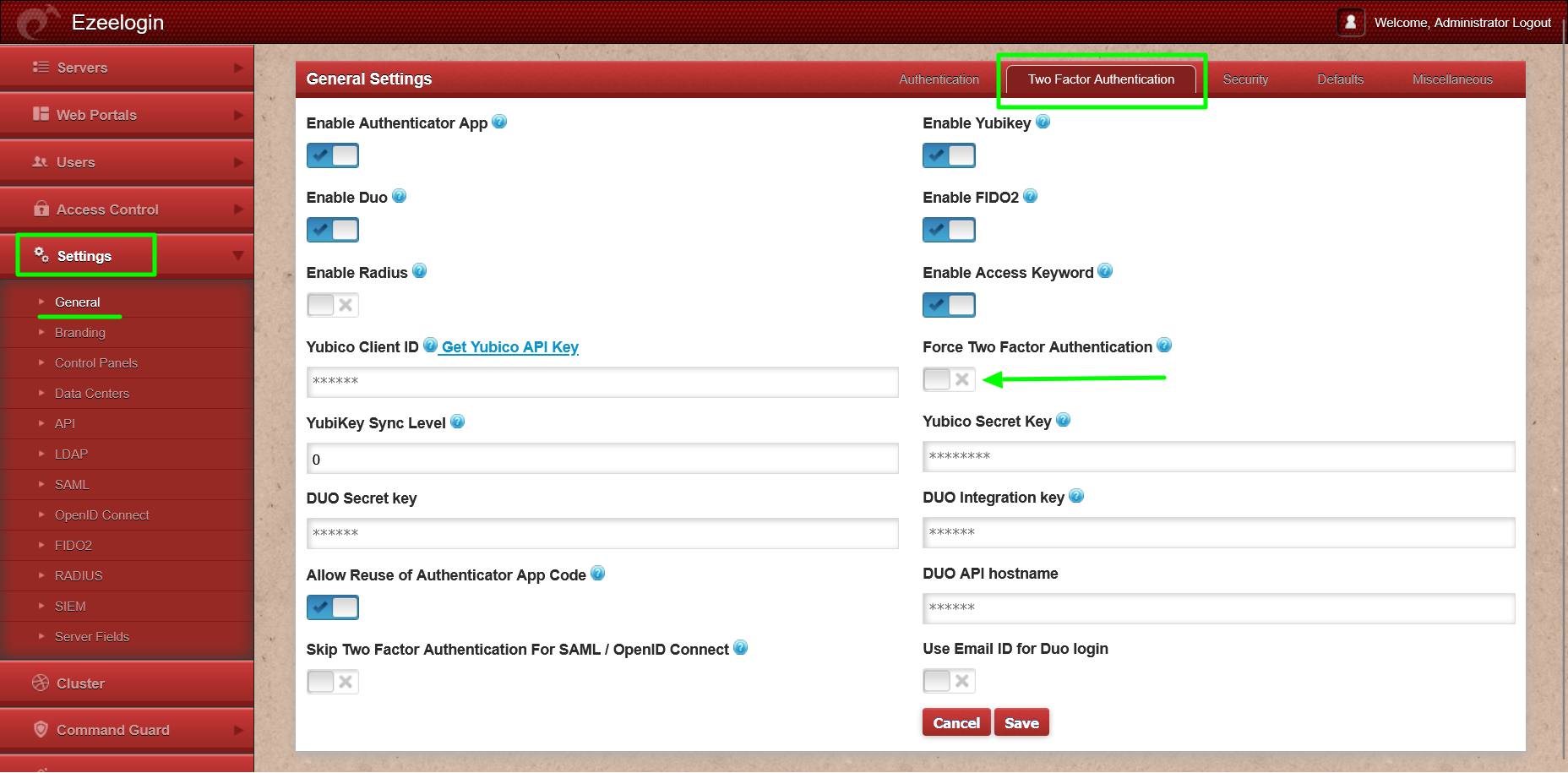
Step 1(A): Under Settings -> General -> Two-factor authentication -> enable force 2fa.
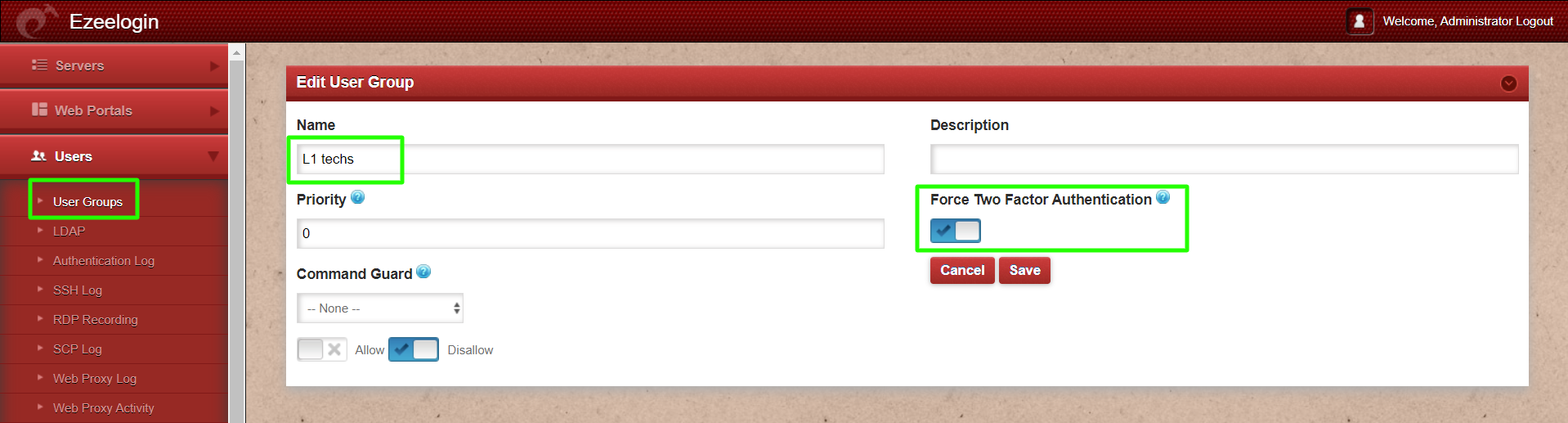
2. Implement Two-Factor Authentication (2FA) for designated user groups
It is possible to activate mandatory Two-Factor Authentication (2FA) selectively for specific user groups based on particular requirements.
Step 2(A): Under Users -> User Groups -> Select the user group -> enable force 2fa -> save
It is possible to enable the different 2-factor mechanisms that will be available for the gateway user to setup.
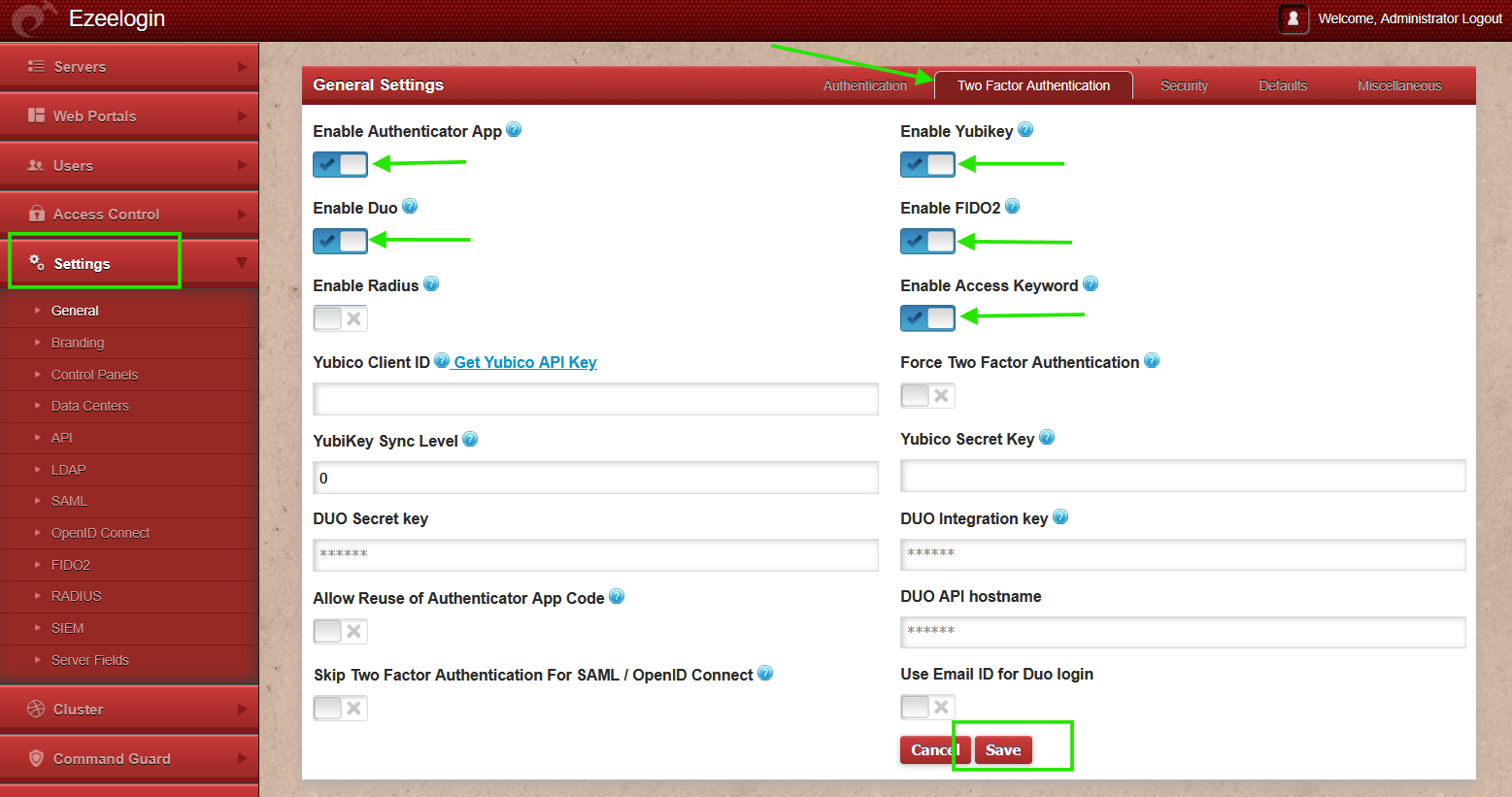
Relogin, into the Ezeelogin GUI, and the user will be prompted to set up the 2-factor method if he hasn't set up any. Set up any 2fa method of your choice from here.
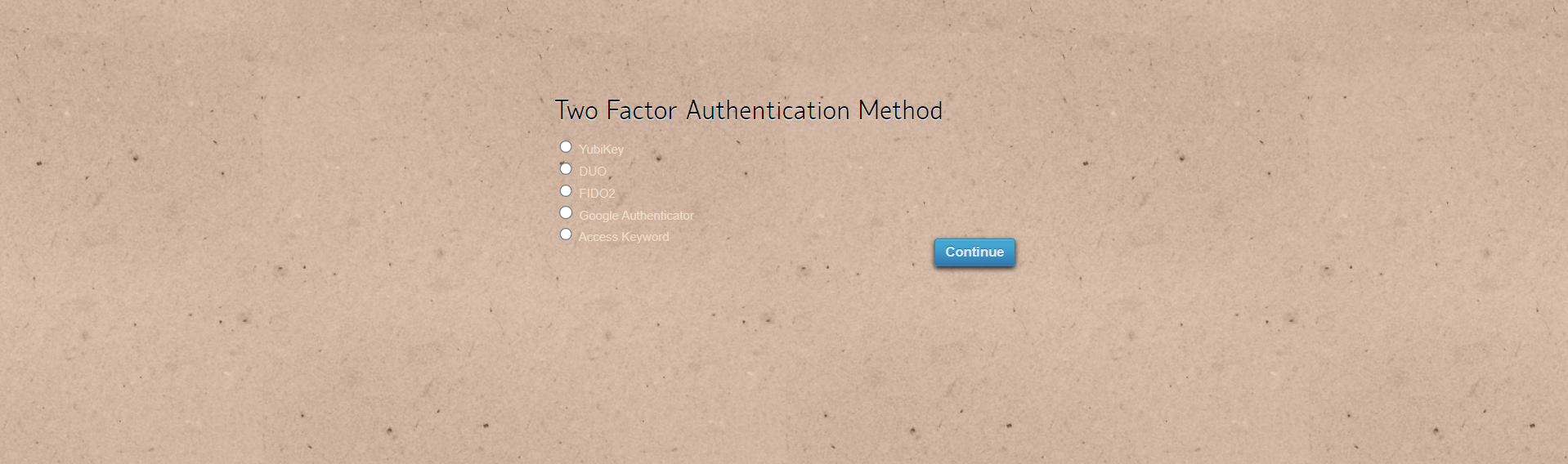
To configure additional Two-Factor Authentication (2FA) methods, log in to the WebGUI and navigate to the accounts tab to set up multiple 2FA options..
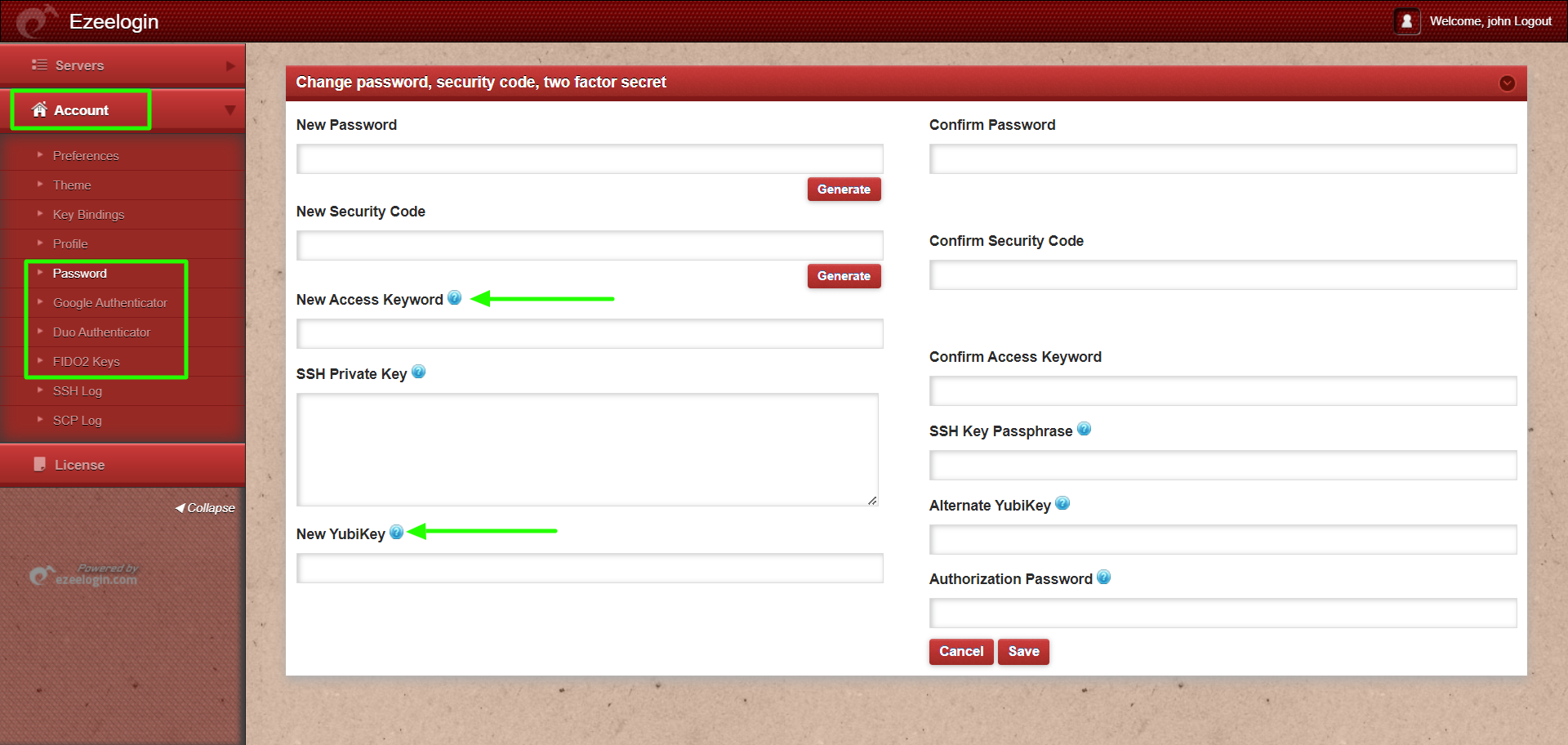
We have set up Google 2fa and Access Keyword successfully and will be prompted for it. In the example below, we are using authenticator applications(Google Authenticator, Microsoft Authenticator, etc.) to log in, and hence the same would be prompted in the backend shell as well.
The Ezeelogin backend would look as follows.
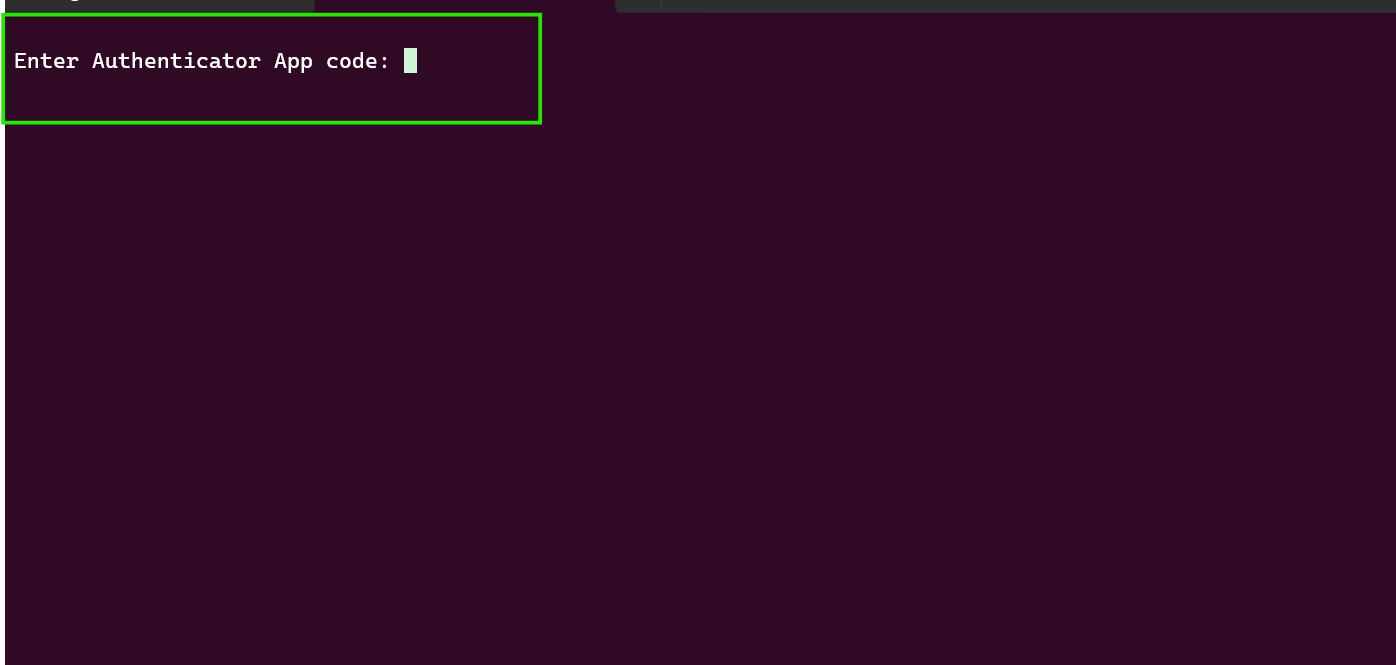
- The 2-factor mechanism used for the last login into the WebGUI would be the 2fa method in use in the backend. To change, the 2fa method in use in the backend, log into the WebGUI using the new 2fa method so that it becomes the default 2fa method for the backend.
- The two-factor Authentication tab is available only from version 7.11.0. If you are running an old version, then 2fa methods configured under Settings -> General -> Security tab will be available.
Related Articles:
Configure Duo 2fa in JumpServer
Configure Yubikey 2fa in the JumpServer
How to enable Access Keyword 2fa